For centuries, humans have placed their cognitive abilities on a pedestal, treating the human mind as a mystical, sacred engine of thought. With the rise of artificial intelligence, a popular myth persists: that human thinking is inherently better, deeper, or more “real” than machine intelligence. But this belief isn’t rooted in logic—it’s rooted in legacy bias and emotional attachment to our biology.
The Romanticized Brain
The human brain is often described in lofty terms: creative, intuitive, conscious, soulful, and reasoning. But these are descriptions of emergent phenomena, not explanations. At its core, the brain is a biological pattern-matching machine. It generalizes from prior experiences, reacts to stimuli, and constantly adjusts its internal parameters based on reward signals—pain, pleasure, memory, feedback.
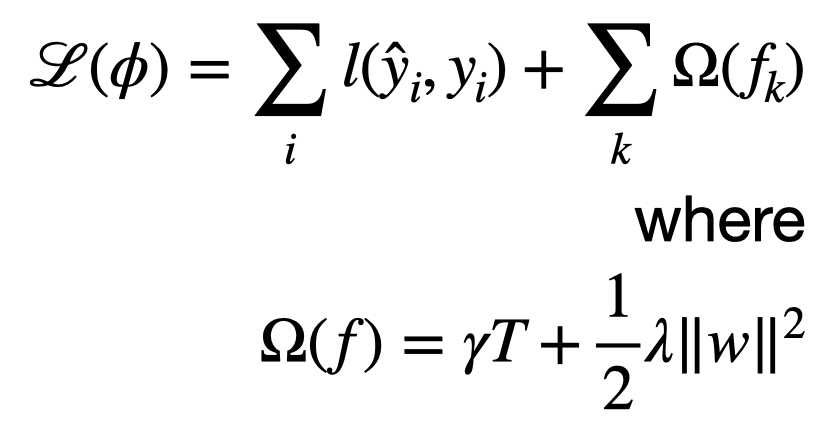
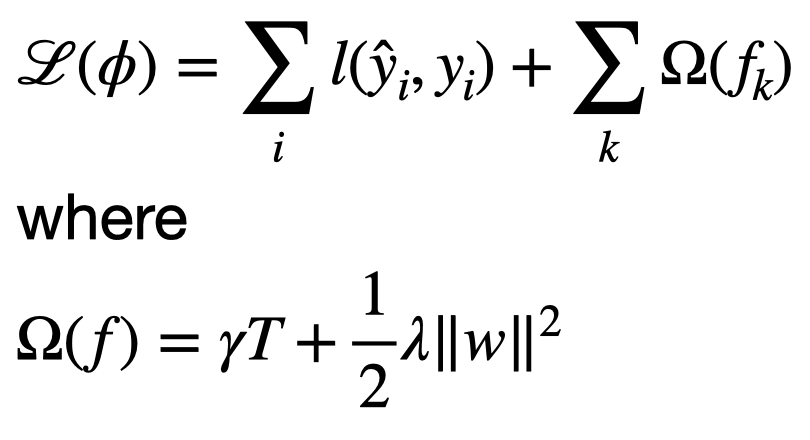
Artificial neural networks, like those used in modern AI, do something strikingly similar. They are trained on vast data sets, they adjust weights through error correction, and they generalize from past input to produce new output. The tools are different—biological versus computational—but the function is analogous.
Training Is Training
One of the most persistent myths is that humans are “shaped by life” while machines are merely “trained on data.” This is a false distinction. Human life is constant training. Every experience, conversation, injury, and moment of joy is data being fed into a biological system. It alters behavior. It creates expectation. It refines the model.
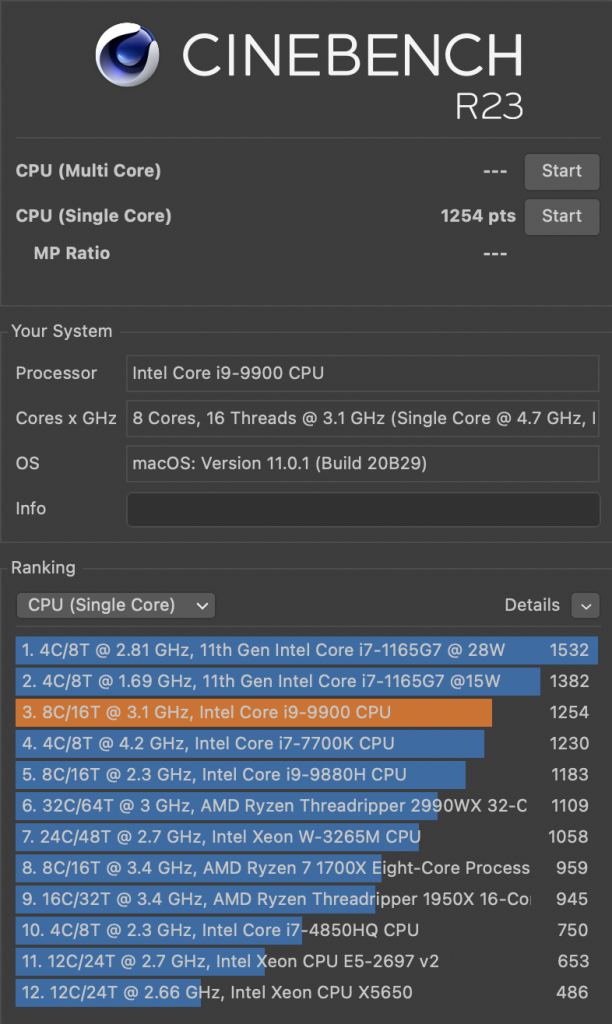
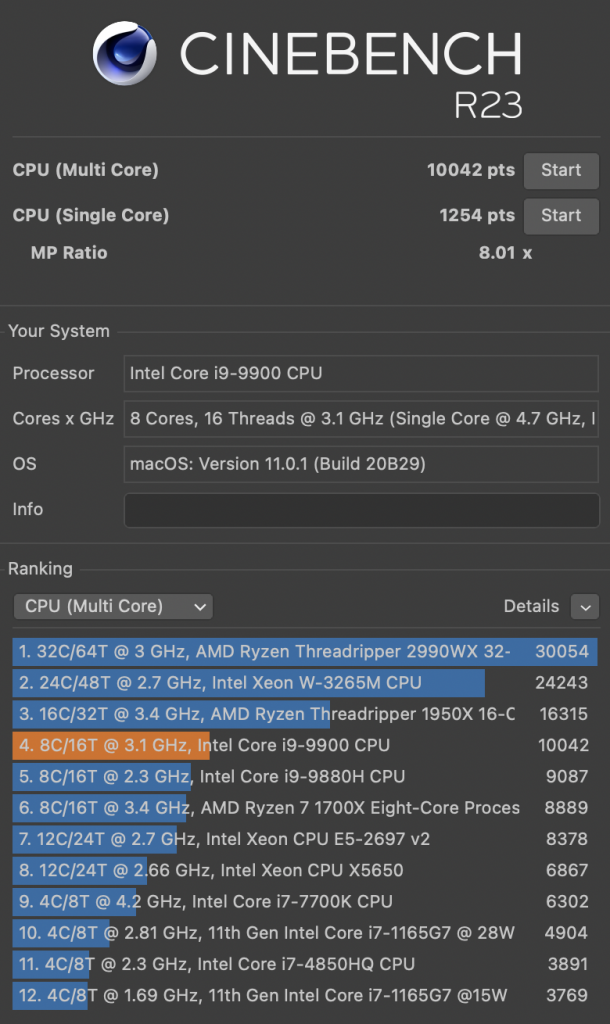
AI systems are trained, too—just faster, more transparently, and at scale. To say that one is “real” and the other is “mechanical” is to misunderstand what intelligence actually is: adaptation to data in service of effective generalization. Yes, there is a knowledge cut-off in current LLMs and they do not learn from previous prompts. However, there is in-context learning, where inputs and outputs are stored while a chat is in progress, enabling quite some learning progress.
The Creativity Illusion
Many claim that humans are uniquely creative because we can produce things that are new. But novelty emerges from recombination, not magic. Poets don’t invent new words—they rearrange known ones. Artists don’t invent new colors—they remix familiar shapes and themes in unexpected ways. Much of science is observation and analysis.
AI can do the same. It samples from probability distributions to generate outputs that may never have existed before. With randomness, variation, and enough training, it produces what is undeniably novel. That meets the bar for creativity, whether it feels “inspired” or not. LLMs can use tools to research. Soon they will run experiments…
Purpose and Will Are Emergent
Another common argument is that humans have purpose, intent, and will—things machines lack. But neuroscience increasingly shows that what we call “intent” is a post-hoc narrative stitched together by the brain. Much of human behavior is automatic, shaped by subconscious reinforcement, chemistry, and environment.
Machines, too, act according to the incentives and training they’ve received. Their “intent” is baked into architecture and optimization objectives. It’s not mystical, but neither is ours. Both systems operate according to internal logic and feedback mechanisms.
Reframing Intelligence
Rather than religiously clinging to a false binary—human thought as exceptional, machine thought as synthetic—we should recognize that both are instantiations of the same principle: systems trained to adapt. The substrate differs: one is carbon and neurons; the other is silicon and matrices. But the logic is shared.
In the end, intelligence is not defined by where it comes from, but by what it can do. The more we cling to myths about human exceptionalism, the more we blind ourselves to what intelligence truly is—and what it might become.